SASE: The future of cybersecurity and networking
This article depicts the Secure Access Service Edge technology which is likely to be the future of both cybersecurity and networking markets.
Hi guys, this is Maël from Orange Ventures. Startin’ is a newsletter that aims to share quality content useful for the startup ecosystem (VCs, startups, fundraisers, etc.) regarding new technologies, investments, financial models, etc.
Imagine taking the best of networking technologies and coupling it with the best of cybersecurity technologies. This seems great, right? This is called SASE, for Secure Access Service Edge.
Gartner expects that 40% of enterprises will have explicit strategies to adopt SASE in 2024, against less than 1% at year-end 2018. Hence, the adoption of this technology is likely to be very rapid. Furthermore, such a technology is even more needed that most security incidents came from the network in 2020, as described in the chart below, extracted from the Security Navigator 2021 report of Orange Cyberdefense.
Before explaining what SASE is, I am going to take you through the traditional architecture, in order to help you understand it and grasp its limits. From there, I will introduce you to SASE and explain you why this is the future of networking and cybersecurity.
📱 Why is SASE appearing?
Until now, the traditional architecture has been using the enterprise datacenter as the focal point for access, as described below. Hence, every time people wants to access a resource, either people are in the office or outside, and either the resource is stored internally or externally, the request is going through the enterprise datacenters, as stressed in the Gartner’s chart below.
This made sense when people were working in the company’s office and were mainly using internal resources. However, times have changed, especially with the COVID-19, where the BYOD (Bring Your Own Device) movement has exploded. For instance, during the second half of March 2020, there has been a 41% increase in the demand for VPN solutions according to the Security Navigator 2021 report of Orange Cyberdefense. This has been coupled with the ever increasing use of external resources. As Marc Andreessen pointed out in 2011, “Software is eating the world” and guess what, it is still true. In 2019, companies with 200 to 500 employees were using approximatively 130 unique enterprise softwares, according to Blissfully. To sum up, today we have:
More user work performed off of the enterprise network than on the enterprise network;
More sensitive data located outside of the enterprise data center in cloud services than inside;
More traffic from branch offices heading to public clouds than to the enterprise data center.
Therefore, this traditional architecture that is routing traffic to and from the enterprise data center make no sense because:
It is not scalable;
It has a bad UX, high latency and costs as SaaS can only be accessed if a user is on the enterprise network or uses a VPN. It can also require different agents such as SWG and CASB, which creates agent bloat and user confusion;
Just a few amount of data is stored on the enterprise data center.
📡 What is SASE?
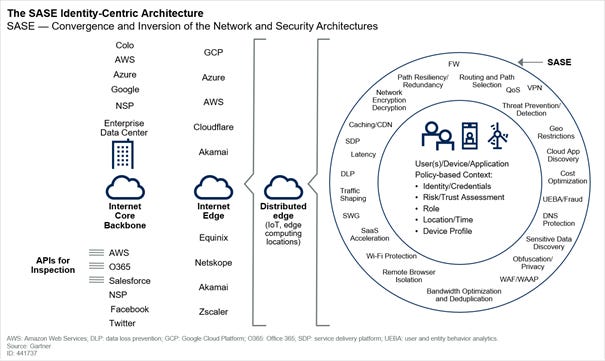
SASE (Secure Access Service Edge) is an emerging offering converging network and security tools within unique cloud-based platform. With SASE, security professionals can specify in real-time the level of performance, reliability, security, and cost of every network session based on identity and context. Hence, SASE will provide policy-based “software defined” secure access. The chart below, also made by Gartner is useful to understand how this works.
With SASE, the enterprise data center is still there, but it is not the center of the architecture. It is just one of the many internet-based services that users and devices can access, as pointed out by the chart below.
Therefore, this technology is based on the zero trust principles. This is an end to end approach to network/data security and a collection of concept, where you never trust, but always verify the user, device, workload or system whether it is inside or outside the organization security parameter. It is based on 3 assertions:
Therefore, this technology is based on the zero trust principles. This is an end to end approach to network/data security and a collection of concept, where you never trust, but always verify the user, device, workload or system whether it is inside or outside the organization security parameter. It is based on 3 assertions:
The network is always assumed to be hostile;
External and internal threats exist at all time;
Every device, user, and network flow needs to be authenticated and authorized.
Hence, SASE relies on:
The identity of the entity at the source of the connection (user, device, branch office, IoT device, edge computing location, etc.).
Real-time context (time of the day, location of the entity, etc.) and continuous assessment of risk/trust throughout the sessions.
Dynamically created security parameter (the security perimeter is dynamically created to be everywhere an enterprise needs it to be. So it is not something fixed in a box at the data center edge)
🔍 What are the SASE’s components?
We identified 3 types of components and capabilities for SASE, depending on their level of importance. Below, you will have more details about it.
🧭 How to analyse SASE offerings?
Breadth of SASE services offered:Some vendors will start with networking-centric functionality, others will start with security-centric capabilities.
Location of the SASE management/control plane: The SASE management console should be delivered as a cloud-based service. Policies should be cloud-managed and distributed to local enforcement points.
Tenancy model: Cloud-native SASE architectures will almost always be multitenant with multiple customers sharing the underlying data plane. Some providers will instead use a dedicated instance per customer. Single tenancy typically results in lower densities with potentially higher costs that are passed on to enterprises. However, some enterprises prefer the stronger isolation of single-tenancy models.
Architecture: Ideally, the offering is cloud-native, built on microservices with the ability to scale out as needed.
Encrypted traffic inspection at scale: SASE offerings must be able to deliver in-line encrypted traffic inspection at scale, ideally delivered from the cloud and without the use of proprietary hardware.
Ability to identify sensitive data and adapt: SASE offerings should understand the context of the data/applications that are being accessed and be able to take adaptive actions if excessive risk is detected.
Granular visibility and detailed logging: SASE offerings should provide granular activity monitoring of the user when accessing applications and services. All activities within a session should be logged, requiring the SASE offering to create and manage distributed logs at scale.
User privacy: SASE vendors should offer the option to not inspect traffic based on policy (e.g. GDPR). This noninspection policy may be combined with remote browser isolation to further isolate the session from enterprise systems and logging.
✔️ Benefits of SASE
Reduction in complexity and costs: SASE allows the consolidation of technology stacks and secure access services to one single provider, so the number of appliances in a branch will be reduced, and the number of agents required on an end-user device will be reduced.
Enable new digital business scenarios: SASE enables companies to make their services securely accessible to third parties without the risk exposure of legacy VPN and demilitarized zone (DMZ) architectures.
Improvement in performance / latency: It is no more needed to go through the enterprise data centers to access cloud-based services, so the performance is improved.
Ease of use / transparency for users: SASE will reduce the number of agents required on a device to a single agent.
Low operational overhead: With cloud-based SASE offerings, updating for new threats and policies requires no new deployments of hardware or software by the enterprise and should allow quicker adoption of new capabilities.
Enable zero trust network access: Network access is based on the identityof the user, the device and the application, not on the IP address or physical location of the device.
Improve effectiveness of network & network security staff: Instead of the routine tasks of setting up infrastructure, network security professionals can focus on understanding business, regulatory, and application access requirements and mapping these to SASE capabilities.
Centralized policy with local enforcement: SASE allows cloud-based centralized management of policy with distributed enforcement points logically close to the entity and including local decision making where needed.
❌ Risks of SASE
Siloed teams, culture and politics: Network and network security teams are typically different siloed teams. Even in information security, the buyers for SWG, CASB and network security may be different. Different teams may fight the adoption of SASE as a matter of job protection.
Complexity: For enterprises that attempt to build their own SASE stack out of disparate vendors and cloud offerings, stitching this together will lead to inconsistent management and enforcement, poor performance, and expensive deployments. A similar problem occurs if the SASE offering is stitched together by a vendor from multiple acquisitions and/or partnerships.
Switching vendors: For some enterprises, the shift to SASE will require a switch in vendors, which will imply the need of staff retraining, development of new skills, and learning a new management and policy definition console.
💰 Which business model for SASE?
As previously explained, SASE is the fusion of network and security services. Whereas network services are mostly licensed by bandwidth, security services are licensed per user, per year. Hence, it is fair to wonder what will be the business model for SASE. According to Gartner, SASE solutions might charge their customers on a subscription basis, based on the number of entities protected — either individual entities (devices, users, apps, systems) or aggregation of entities (branch office/IoT and edge locations).
👨💼 Which actors could potentially develop SASE?
3 types of players could develop such solutions, but all have weaknesses that must be taken into account, to be able to find who will be the next big players on this market.
Traditional network-centric providers: The problem with them is that they have a lack of security expertise, so there is a risk of higher costs and/or poor performances. They have a lack of understanding in data context, which is critical for prioritizing risk, and adapting the access policies accordingly.
Traditional security-centric providers: As for them, the problem is that they may not have the full SD-WAN functionality expected of a leading WAN edge solution. They do not have a cloud-native mindset.
Startups: Finally, for them, it could take time to have relevant SASE offerings due to high barriers to entry and their lack of resources to conduct M&A transactions of network or security solutions to speed up this process.
👨💻 What are the alternatives to SASE?
As for now, the 4 following alternatives to SASE exist:
Status quo using a hardware-based branch office
Build SASE yourself via service chaining: This approach risks unmanageable complexity, high costs and high latencies.
Provider-orchestrated service chaining: Turn to a dominant provider in networking, network security or a carrier and let the vendor perform the service chaining needed on behalf of the customer. Here the risk is that we do not know who manages and controls management consoles, and there is disparate policy frameworks.
Get the Network as a Service from one vendor and the Network Security as a Service from another one: This has the advantage of solving organizational politics, but with higher complexity and costs than if a single SASE provider was used.
💻 SASE market
No compelling market studies to compute the market size and its forecasted growth were available. However, as the SASE market is at intersection of the Network as a Service market and the Security as a Service one, looking at the size and CAGR of both market can help you get a rough idea of the SASE market. According to MarketsandMarkets, the Global Security as a Service market is expected to grow from $11.1B in 2020 to $26.4B in 2025 at a CAGR of 18.9%, whereas the Global Network as a Service market is expected to grow from $4.3B in 2020 to $21.7B in 2025 at a CAGR of 38.3% during the forecasted period.
Even though, no information regarding the market size is publicly available, Gartner has published a few figures that are also helpful to understand how this market is evolving. According to Gartner, 40% of enterprises will have explicit strategies to adopt SASE in 2024, against less than 1% at year-end 2018. This means that market adoption will be very rapid. At the same time, 20% of enterprises will have adopted SWG, CASB, ZTNA and branch FWaaS capabilities from the same vendor by 2023, against less than 5% in 2019.
All these elements are proofs that this market is a large one, with strong forecasted growth, due to the rapid adoption of the technology.
💵 Deals on the SASE market
Two types of deals are likely to occur on the SASE market.
The first one consists in big players in network or security buying missing parts of their offering to create a SASE offering. This type of deals is expected to represent the most important part in the short run. Indeed, Gartner expects further consolidation and acquisitions over the next 5 years, from network and security players trying to build up a SASE offering. Some companies have already started partnering. For instance, Silver Peak and Netskope have recently decided to join forces to be able to offer a SASE solution.
The other type of deals consists in the acquisition of full SASE solutions. For instance, in July 2020, Fortinet acquired Opaq, a Series B startup providing a SASE offering, that previously raised a total of $43.5m. This is the only SASE provider that has been acquired so far and this is related to the low level of maturity of this market. Thus, we can expect much more acquisitions on this market on the long term.
🗺️ Market mapping
Now that you have a good understanding of what SASE is, I let you enjoy the mapping below:
About Orange Ventures
Orange Ventures is a venture fund investing in areas of Orange expertise and beyond: we invest in startups with ambition to imagine, design and develop innovative solutions, disruptive technologies and business models of tomorrow.
With 350m€ assets under management Orange Ventures is in the top 10 corporate ventures in Europe with the investment strategy focused on helping future global tech champions, fostering innovation in the Middle East & Africa and supporting new sustainable and responsible business models.
The fund has set financial objectives in line with VC industry standards, leveraging proximity to the Orange Group as a main differentiator in its proposition to startups.